CMITE: China's tech arms show
The upcoming annual trade show in Beijing, which aims at the military and other civilian security services, demonstrates the vibrant nature of China's digital military-industrial complex.
As the China Beijing Military Intelligent Technology Expo (CMITE) enters its 11th edition this May, we thought it worthwhile to examine the event and its exhibitors in greater detail.
Traditionally, a significant number of Chinese cybersecurity firms participate, showcasing their products and services to China’s security and military sectors. This expo features once again a diverse lineup of hundreds of suppliers, offering products that range from cutting-edge innovations to more conventional solutions.
The expo is where China’s Military-Civilian-Industrial Complex converges. From startups to established firms, they are all vying for contracts with government agencies or state-affiliated companies. One exhibitor, the cyber security company Antyi, even quotes president Xi Jinping in their profile: “You are also a national team, although you are a private enterprise” (‘national team’ is usually used in connection with State Owned Enterprises. ).
That shows these companies, despite at times privately operated, don’t stand apart. They are integrated into China’s arms development process (not too different from how the US handles it, just on a bigger scale ).
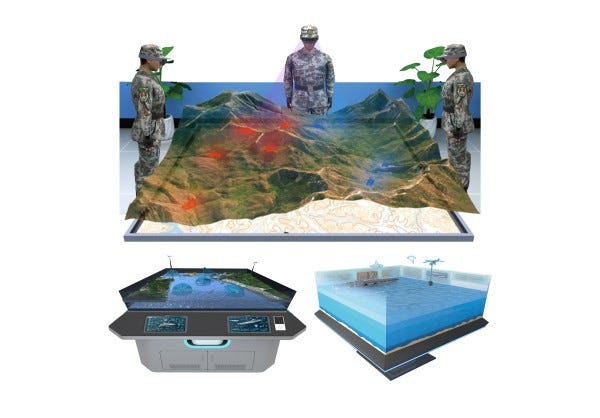
As in previous years, we anticipate a strong focus on drone technology, like jammers and drone defense systems. AR/VR-training systems have also gained prominence, with immersive simulations for driving tanks, flying helicopters and drones, assault rifle training, and terrain navigation. And it can all be done without leaving the classroom.
Exhibitors will also present exoskeleton systems, alongside more practical solutions like electronically assisted combat first aid, secure field communications, and mass-data storage.
Unsurprisingly, AI integration dominates the narrative. Whether it’s truly effective or not, is of course always hard to determine from marketing material. Artificial Intelligence remains the buzzword of choice at the moment, much like in other industries around the world.
While not the only event of its kind in China, CMITE’s location in Beijing lends it added significance compared to similarly sized exhibitions elsewhere. As a company you can be assured that the main decision makers within the PLA ( army ), the PLAAF (the air-force), the PLAN (the navy) and other security organizations will be here.
For us, the cybersecurity and surveillance aspects are particularly interesting. A disclaimer: our analysis is based solely on the official CMITE website’s exhibitor pitches, including the (at times rather low res screenshots of products). So the actual capabilities of these companies may differ from their marketing claims, a common occurrence in this sector. Still, the width and variety of tools on display make for fascinating observations.
The website lists 111 vendors, though the actual number is likely higher. But let’s see what is on the menu.
1. 乾图科技: AI driven combat simulation and scenario analysis
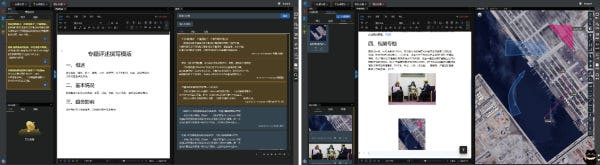
Qiantu Technology from Beijing provides a ‘War game simulation’ machine that can be used by armies to plan campaigns or singular operations, fed with past combat statistics and scenarios to see how it plays out.
According to the brief on the website the company is specialized in ‘spatio-temporal intelligent decision support’ and has been involved in many military planning and tactical exercises.
One of the screenshots shows a simulation for ‘establishing a beach head’ at Taiwan, after the action of the US and the Taiwan government has led to a final escalation at the Strait and China needs to ‘assert its national sovereignty’.

The excerpt states “Qianhui integrates AI with traditional plotting functions, leveraging AI image recognition, semantic understanding, natural language processing, and other technologies to achieve functions such as rapid plotting, text-image conversion, and intelligent plotting suggestions. Combined with AI animation generation technology, it creates an immersive broadcasting effect.”
They are not the only suppliers for such solutions of course and the trend to offer AI driven combat analysis, planning and training products is quite evident as it appears in several listings. There seems to be a general hope that AI might help to overcome planning short-comings of the PLA, which lacks recent real-world combat experience.
2. 道达天际: Big Data + OSINT analysis
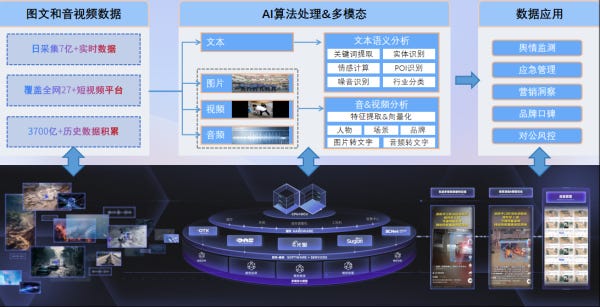
The company Beijing Daoda Tianji Technology, founded in 2002, offers an AI enhanced big data analysis platform, that uses OSINT to gather information globally and package it for analysis. The system is built around the DAOSMOS ‘big model’ that helps to process, categorize, summarize and prioritize this collected information.
It is sold as an pro-active intelligence analysis tool, that keeps its user up to date and points him towards future developments etc. The proliferation of Big Data analysis in combination with large scale data scrubbing from the global net is a development we have observed also in the realm of cyber surveillance. The screenshots below show the mass-data scraping and analysis tool in a style not too different from offerings of western competition.
3. 中科金联 and 指掌易: Keeping tabs on soldiers
As we have already explored in our conversation with Dr. Valentin Weber, the PLA's paranoia of their soldiers and officers leaking important information, by increased use of smartphones and social media is well known.
Companies like Zhongke Jinlian from Beijing offer systems to keep an eye on the behavior of individuals online and offline. These systems try to analyze the mental state of soldiers via real time visual footage from surveillance cameras and their online posts. It markets their technology as ‘non-contact’, so no direct interaction with the individual is needed and their analysis system works at scale.

Other exhibitors offer a even more comprehensive option. The company 指掌易 provides more hands-on surveillance of digital devices owned by PLA members. How successful this kind of software is in the end, needs to be determined. But the general paranoia of military leadership of ‘the human point of failure’ is for sure good business (and probably some snake-oil).
4. Stonehenge: China's self proclaimed ‘Palantir’ competition
Next up is the company 中科世通亨奇, Zhongke Shitong Hengqi Technology (Stonehenge). This Beijing based outfit was founded in 2016 and has close ties to the Chinese Academy of Sciences (CAS), according to their own advertisement material.
They are marketing a tool called ‘Lingjing Tiangong’, which is described as a Data-Driven Intelligent Decision-Making Operating System. According to Stonehenge themself the 12 core apps are benchmarking against the Palantir Platform (Foundry + AIP).
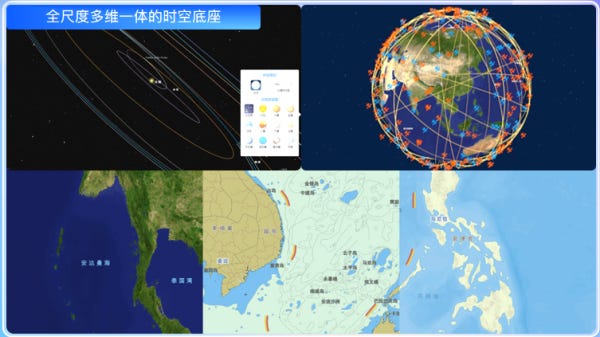
“Lingjing Huanyu primarily utilizes digital earth technology, employing wide-area data collection and the integration of comprehensive information (with the ability to access internal information sources) to form a high-value holographic twin data warehouse. By analyzing data to understand phenomena, it has constructed a transparent battlefield for key regions. Currently, Lingjing Huanyu has completed the construction of transparent battlefields in important directions, and has continuously accumulated 105 data items across 9 major categories and 38 subcategories, totaling approximately 1000TB, with a core focus on environment, targets, personnel, situation, events, and data.”
These kind of systems are not particularly new, and there is a wide range of providers (there are even free variants out there). However, aired with the right amount of infrastructure and enough sensors, these tools can naturally be very valuable and powerful in the right hands.
5. 丈八网安: Network range service provider
As expected, network range service providers are also on display amidst the exhibitors (though not as plenty as you might suspect). Big players like Cyberpeace are either missing or not on the website. One provider we do find is Zhangba Network Security (or Zeta Byte Network Security).
The company has received investments by the Guangzhou provincial government in the past and offers a modular Network Range setup, priding itself of having a big R&D department to deliver cutting edge products. The ‘Network Simulation Engine’ (ZBOS) is also the underlying foundation of their ‘Sand-table’ product to design and conduct complex network attack and defense scenarios.
“The system's greatest technological highlight lies in its full utilization of discrete event digital simulation technology, enabling the simulation of a large and complex network environment with low resource consumption, and accurately modelling all elements involved in cyberspace attack and defense. Furthermore, the system leverages AIGC intelligent agent technology to assist and replace decision-making, achieving dual-mode simulations: ‘person inside the ring’ and ‘person outside the ring’.
6. 觅熵科技: Tracking enemy assets via OSINT
Another interesting service is provided by the company Mizarvision. Their aim is to provide an AI enhanced database and search system that tracks military assets globally based mainly on OSINT information scraped from the internet.
Targeting key industry sectors globally such as defense, finance and energy, it integrates multi-source and multi-modal, open source, commercial sensor data, This includes but is not limited to daily global medium- and high-resolution satellite data, ADS-B, AIS, and other real-time activity data. It provides key industry target tracking based on open source data, demonstrating excellent performance in terms of coverage quantity, coverage scope and timeliness. Their flagship product is called SPARK.
The SPARK platform is described as: “Based on its real-time acquisition and heterogeneous fusion capabilities of multi-source data, Seeking Entropy provides: ① global intelligence observation sites, dynamic observation areas for strategic targets worldwide, and dynamic observation areas in the Russia-Ukraine conflict; ② the construction of multi-source observation data for clients based on these dynamic observation sites, such as linking military targets, bases, events, and sensor resources; and ③ an intelligence platform based on these observation sites and data. Users can use this platform to acquire potential global military intelligence areas and conduct correlation analysis to uncover in-depth intelligence information.”
7. 中科天玑: Cognitive warfare
Last but not least we run into a well known ‘usual suspect’: GoLaxy (Zhongke Tianji Data Technology Co.) The company got some attention end of last year, when some internal documents were leaked about their ‘cognitive warfare’ platform. This included setting up sophisticated networks of ‘digital twins’, to influence discussions on social media channels and spoofing known names from US politics and media. All with the help of Deepseek. Read up on this crazy story here and here.
Despite this reveal, the company is still alive and kicking, and apparently ready to step back onto the stage, offering their services. Core business of GoLaxy is of course big-data acquisition and analysis, especially with the focus on ‘global opinion monitoring’. That puts them into the same mold as companies like Beijing Wisdom Starlight (istarshine) and their ‘Public Opinion Secretary’ system we reported on last year.
What is missing though is a direct offering of a product as was described in the leaked documentation, though it is not surprising that this might not be on display in publicly accessible documents.
The language in their marketing material hints toward them marketing their services directly to the Chinese security services: “At the national security level, the Tianluo Platform strengthens counter-terrorism and intelligence response capabilities by tracking social media in real time, identifying sensitive topics, and issuing early warnings of leak risks, geopolitical conflicts, and extremist activities.”
Conclusion
While the 11th CMITE appears to follow closely in the footsteps of its predecessor, the event remains a compelling snapshot of China’s evolving security landscape. This year’s exhibition has already showcased a strong focus on lasers, drone and counter-drone technologies, surveillance and counter-surveillance systems, secure field communications, and extensive virtual training environments.
What stands out however, is the persistent emphasis on big-data analysis for both combat scenarios and global opinion monitoring. This signals a clear intent by Chinese security agencies to extend their gaze beyond national borders, assessing the broader impact of their actions. The integration of AI with OSINT (Open-Source Intelligence) is poised to provide valuable insights across all phases of potential combat operations; before, during, and after.
Another notable trend is the heightened scrutiny of soldiers’ social media activity, reflecting a lack of trust in their adherence to established protocols. AI is still applied almost to every product even if its application might be more analog than digital, but this is the way of marketing.
One surprise is the relatively modest presence of cybersecurity firms among the exhibitors. Though, the list may not be exhaustive and more information could still emerge at the event itself. At the very least, 360智语 is returning, having made its debut only last year.
Now, we are aware that a lot of the data we could see on the official homepage is of course often from last year, as the exhibitor announcements won't show the latest tech, but it still gives a good overview of where the journey is going. Most of those tools seem to be squarely aimed at the Chinese market. But as time moves on and China is getting more confident, it would not be surprising to see these brands and tech proliferating along the BRI.