Deep incursions and safe grounds.
A recent wave of investigations and disclosures—from Google, Hunt.io, and others—highlights the growing sophistication of Chinese cyber operations, which now extend far beyond its own borders.
Disclaimer on 02 March 2026: We dropped the ball on this one slightly. The Hunt.io report came out already in January, so it was not coinciding with the Google report. Apologies.
Just days ago, Google’s Threat Intelligence Group (GTIG), in collaboration with Mandiant and other partners, exposed a well-established network of command-and-control (C2) entities. These operations exploited Google Documents as their operational platform. The primary targets were major telecommunications companies across multiple countries, with attackers focusing on extracting personal customer identifiers—likely for tracking purposes.
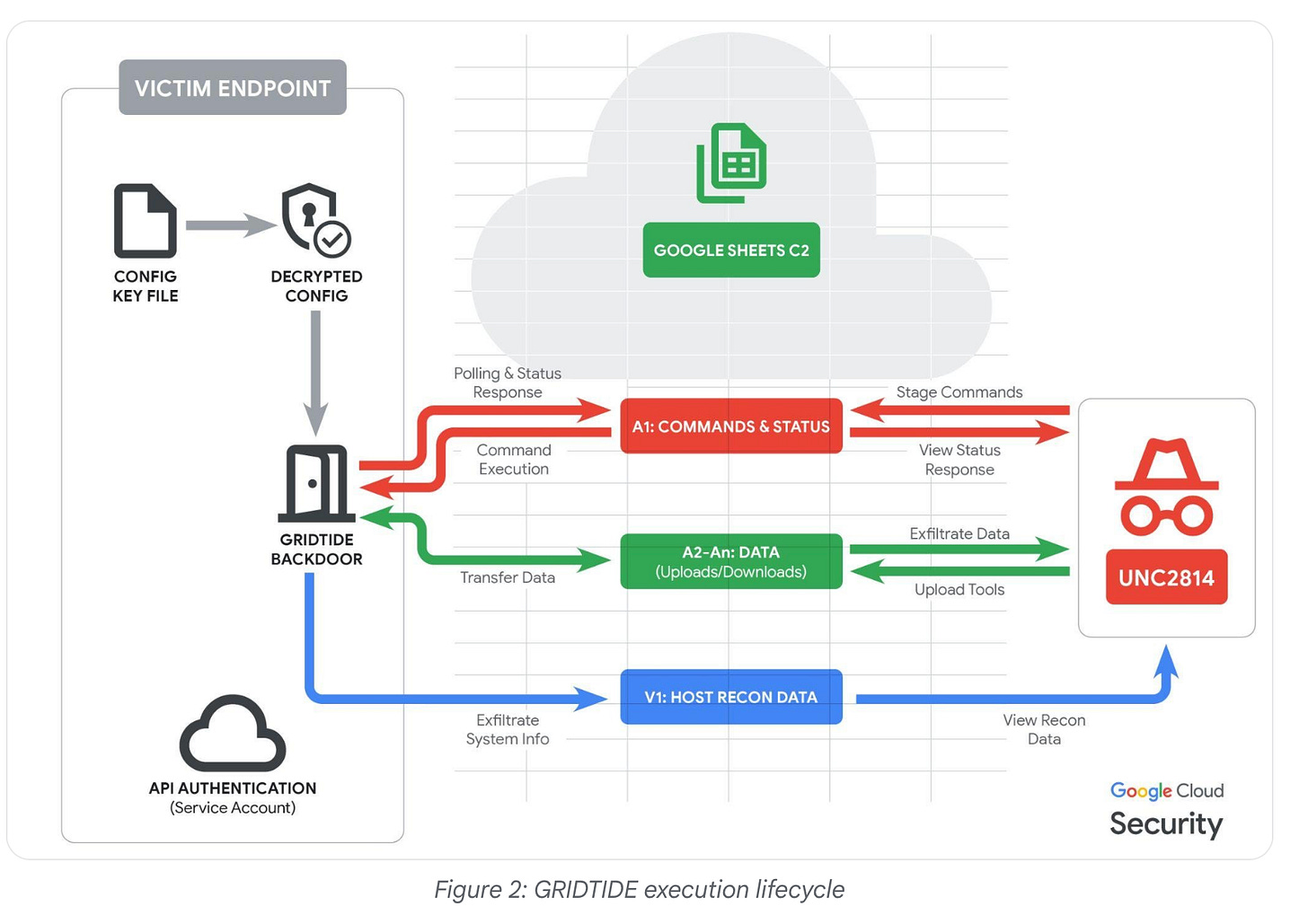
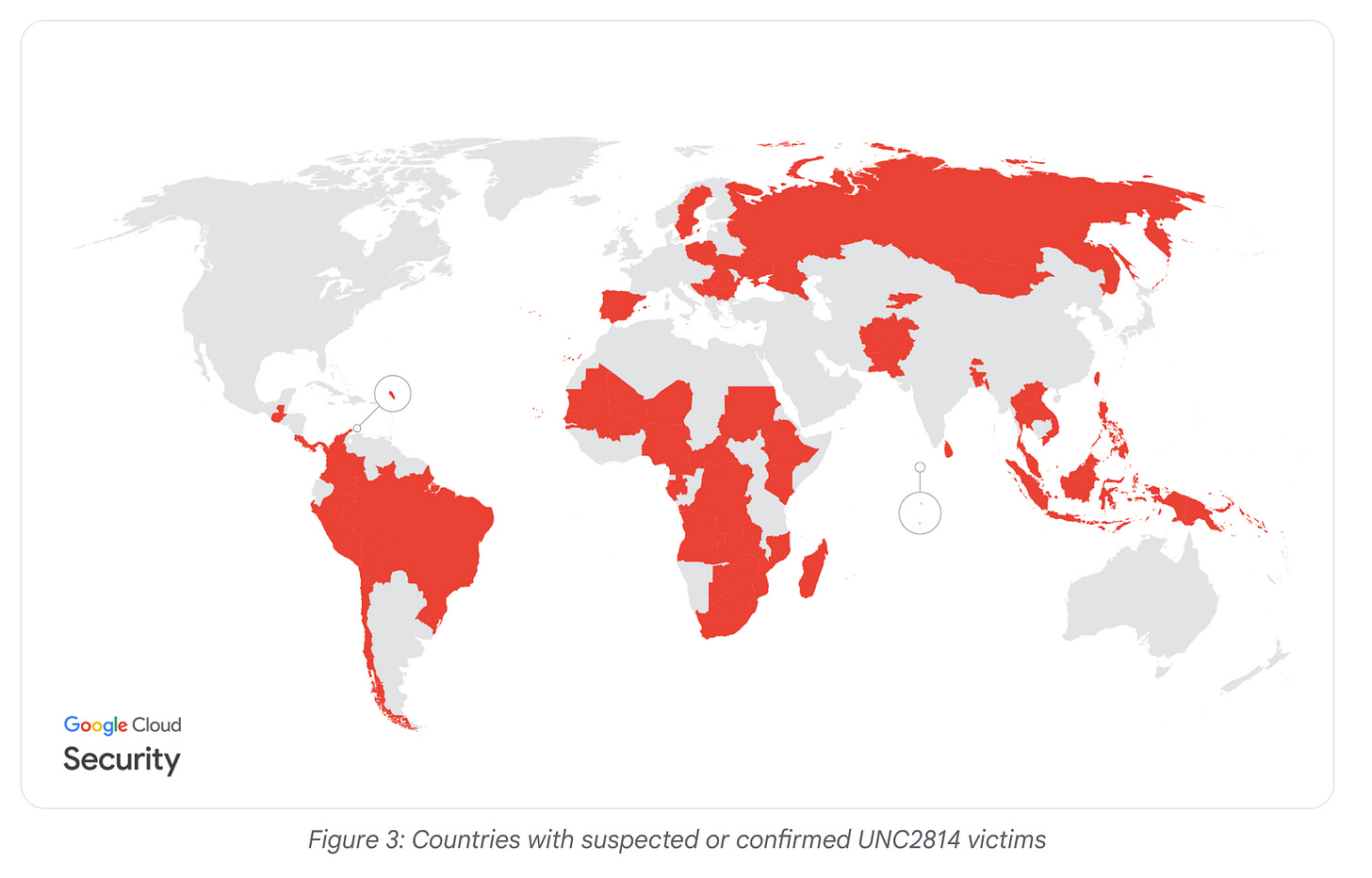
Based on operational traces, GTIG attributed the campaign to UNC2814 (also known as “Gallium”), a sophisticated but elusive Chinese APT group. While the report doesn’t specify how initial access was gained, it’s clear that Google Documents were repurposed as C2 infrastructure, bypassing automated network surveillance. GTIG and its partners named this backdoor “GRIDTIDE.” Data exfiltration occurred via SoftEther VPN, enabling operators to extract call records, monitor SMS traffic, and track individuals using methods typically reserved for law enforcement. The report offers few details on specific targets or countries, but it does mention 53 victims in 42 countries, with signs of infection in entities across 20 additional countries. This isn’t a targeted operation—it’s a dragnet.
Google has clarified that this campaign is unrelated to the earlier breach of US telecommunications infrastructure, widely attributed to “Salt Typhoon.”
It is clear over the past few years that Chinese security services are increasingly looking beyond its borders and run big data acquisition operations that feed a ever growing big-data analysis system, powered by the steady improvement in Artificial Intelligence. We reported on it.
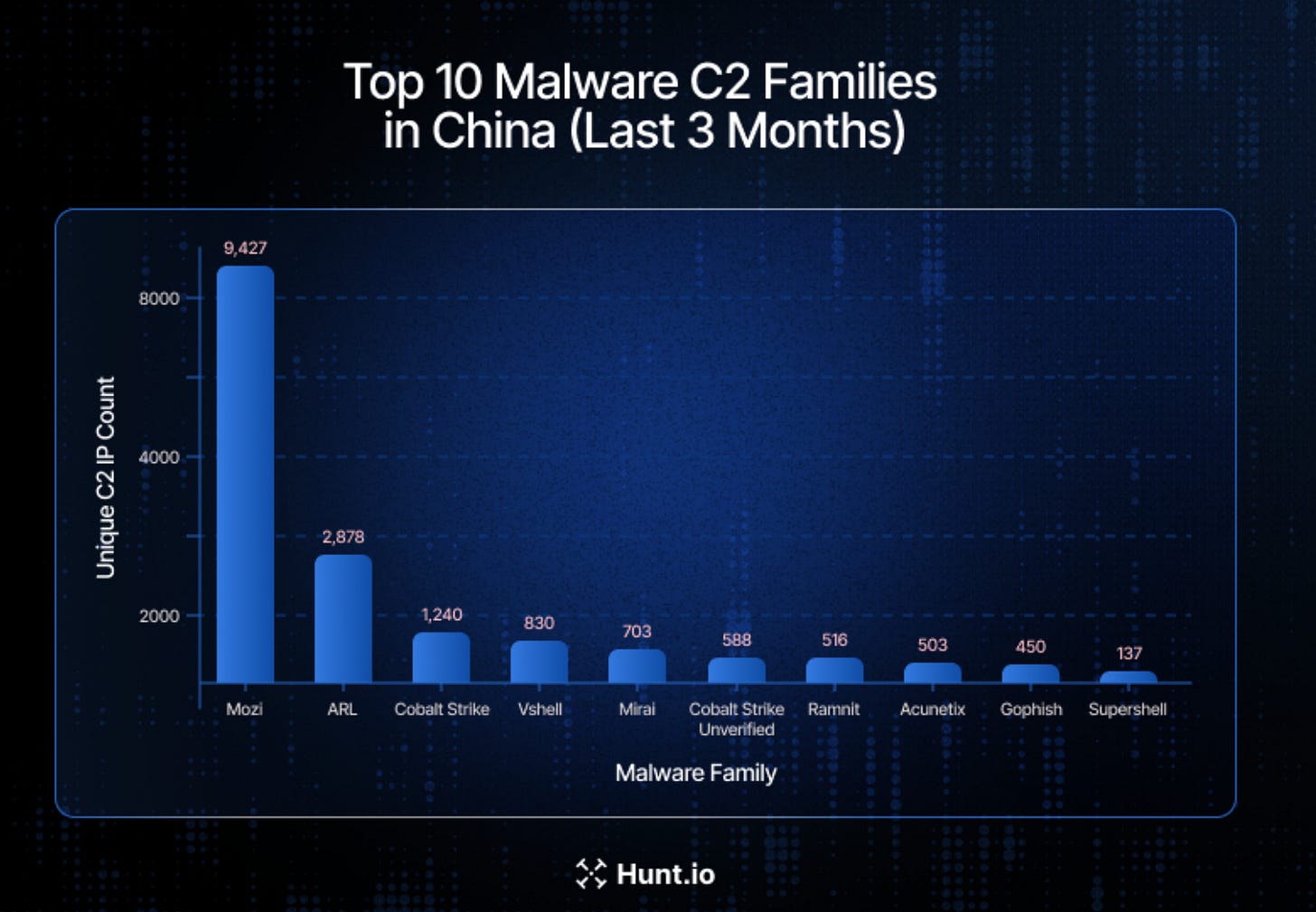
Less than 48 hours later, Hunt.io reported discovering over 18,000 C2 servers for malware mapped to Chinese “high-trust” networks, including CERNET—the backbone for many of China’s top universities. While this doesn’t necessarily imply state-backed APT involvement, it does suggest that both state actors and ordinary cybercriminals may be exploiting China’s sometimes lax network security. The Great Firewall may deter foreign actors from efficiently using C2 servers in China, but domestic operators turning outward face fewer obstacles.
Hunt.io identified a small set of prolific frameworks, with MozI leading by a significant margin, followed by Cobalt Strike and VShell—all tools commonly used by Chinese actors. Botnet C2s, particularly Mozi and some Mirai variants, were also prominent. The report notes: “C2 infrastructure dominates malicious activity (~84%), far exceeding phishing infrastructure (~13%), with open directories and public IOCs together contributing less than 4%.”
Among commercial cloud service providers, China Unicom and Alibaba Cloud (Aliyun) hosted the highest volume of C2 activity.
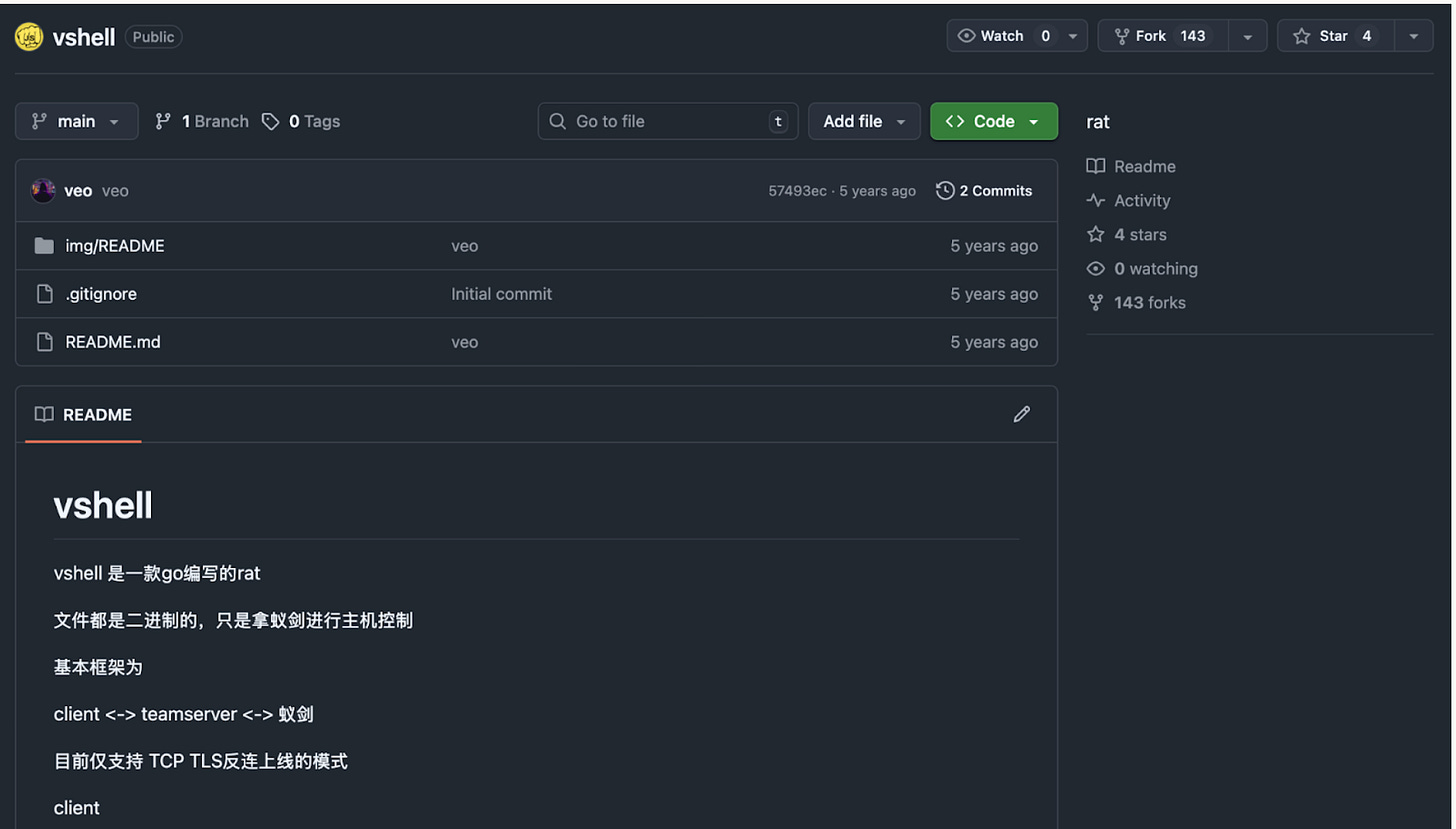
Talking VShell: Silas Cutler from Censys and Ctrl-Alt-Int3l have independently published a deep dive into VShell, a Chinese-language alternative to Cobalt Strike. It was used in a wider attack against academic institutions in Vietnam, among other targets. Following the familiar pattern of building on existing ideas while improving them, both reports are well worth a read: HERE and HERE.
Conclusion
It’s unclear whether the increase in detailed reporting or a genuine expansion of Chinese threat actors’ operational footprint is driving this trend—likely, it’s a mix of both.
What is certain, however, is that China’s massive network infrastructure provides a fertile ground for both APTs and ordinary cybercriminals. While the latter may still fear Chinese law enforcement—especially if they target Chinese citizens or companies—APTs can operate with confidence, knowing the government will protect them as long as they remain behind the country’s veil. And if international complaints grow too loud, Beijing can always claim to be hunting down “mere criminals.”
Of course, it has to be seen how this cases grow in the future, if reporting will increase or subside again. After the revelation that “Palo Alto” has explicitly refrained from naming China as a potential source of adversarial operations because of fears of economic reprisals doesn't instill a lot of hope.